
eBook: Cybersecurity in Smart Factories – Spring Edition
This eBook includes stories on the steps to developing a smart factory and why smart buildings are often insecure.

This eBook includes stories on the steps to developing a smart factory and why smart buildings are often insecure.

This eBook, full of our popular Throwback Attacks, includes stories on how a Florida teen infiltrated the DoD and much more.
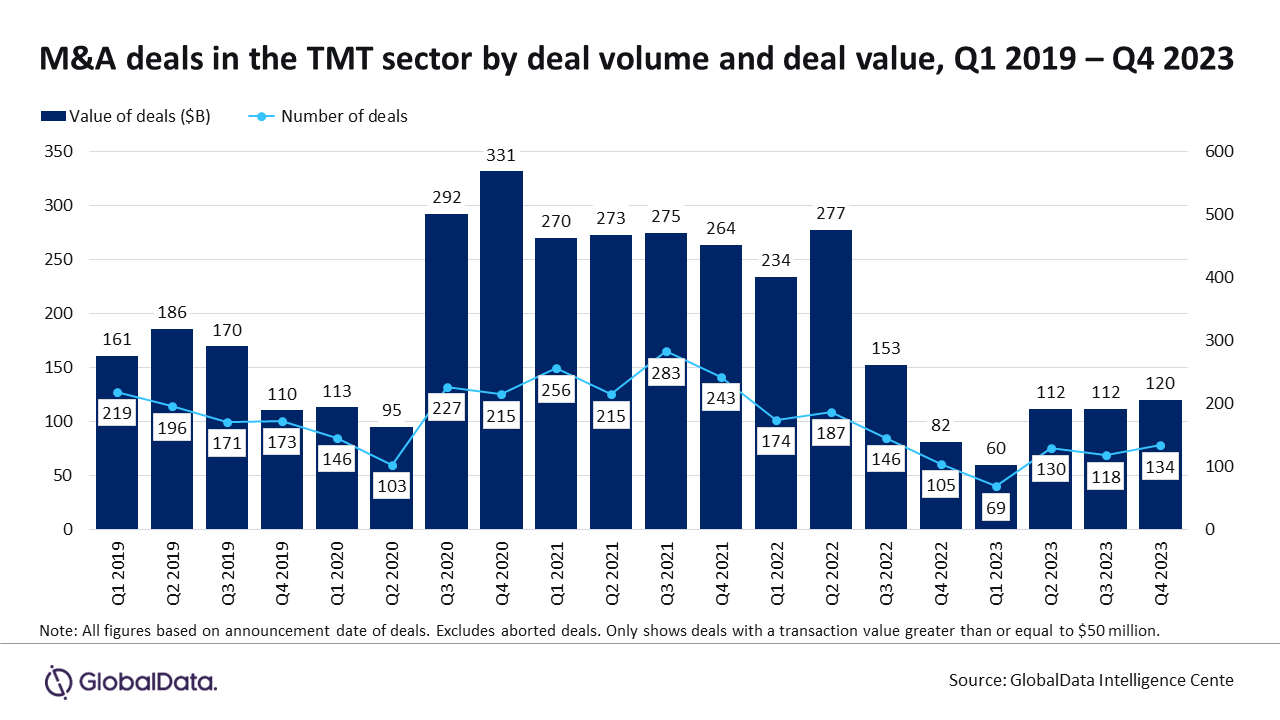
With escalating cyber threats, companies are prioritizing investments in cybersecurity capabilities, leading to a surge in M&A deals in 2023.

This eBook includes stories on how NotPetya took down shipping giant Maersk and which OT/ICS devices are the riskiest.

The top 5 articles from January 2024 covered everything from SCADA security to IT/OT convergence to operational lifecycle management.

Our top 5 pieces from December 2023 covered bringing SOC/SOAR standards to OT, mobile device management and more.

In this highly interactive webcast, Jeff McDaniel of Airgap will demonstrate how easy it is to close the identity gap for OT.

Already used regularly for IT security, a converged IT/OT SOC can give you greater visibility across your operations and help you defend against outside threats.

This eBook includes stories on how you can detect ransomware faster and how tabletop exercises can help prepare your employees.

When evaluating an organization’s security objectives, you should understand how those objectives align to not overshoot your security target.

This eBook includes stories on the steps to developing a smart factory and why smart buildings are often insecure.

This eBook, full of our popular Throwback Attacks, includes stories on how a Florida teen infiltrated the DoD and much more.
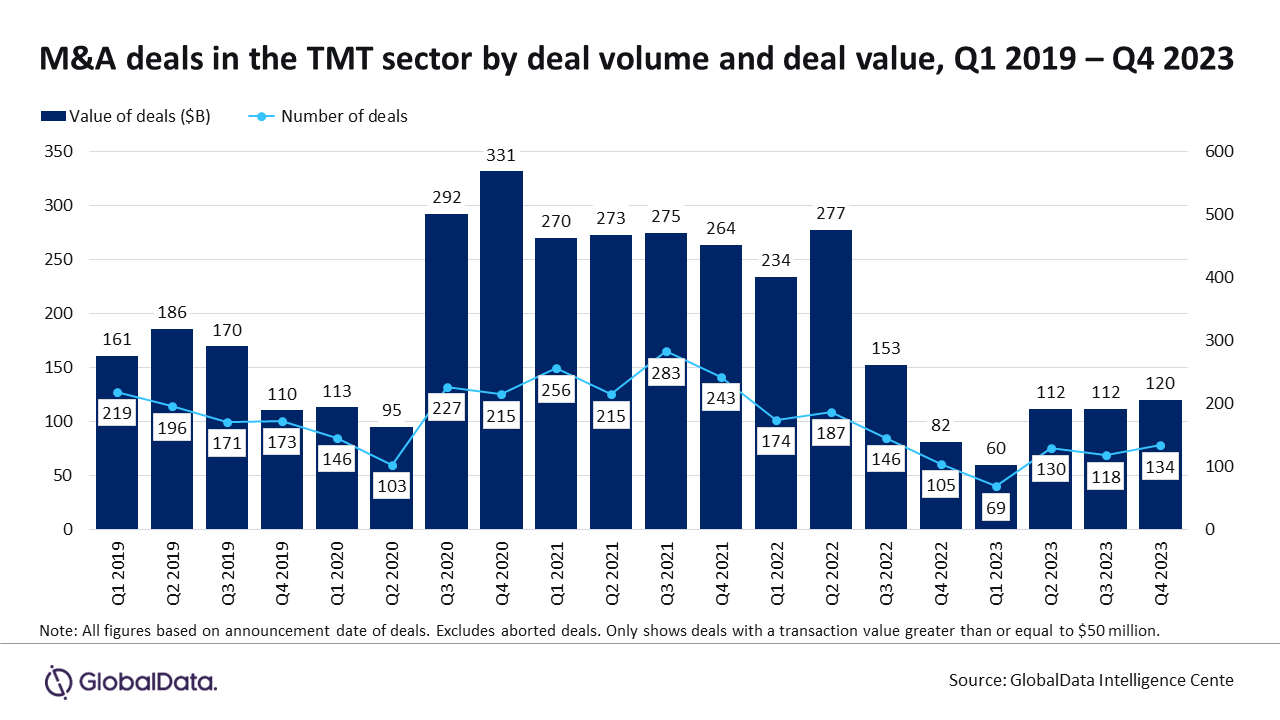
With escalating cyber threats, companies are prioritizing investments in cybersecurity capabilities, leading to a surge in M&A deals in 2023.

This eBook includes stories on how NotPetya took down shipping giant Maersk and which OT/ICS devices are the riskiest.

The top 5 articles from January 2024 covered everything from SCADA security to IT/OT convergence to operational lifecycle management.

Our top 5 pieces from December 2023 covered bringing SOC/SOAR standards to OT, mobile device management and more.

In this highly interactive webcast, Jeff McDaniel of Airgap will demonstrate how easy it is to close the identity gap for OT.

Already used regularly for IT security, a converged IT/OT SOC can give you greater visibility across your operations and help you defend against outside threats.

This eBook includes stories on how you can detect ransomware faster and how tabletop exercises can help prepare your employees.

When evaluating an organization’s security objectives, you should understand how those objectives align to not overshoot your security target.
Keep your finger on the pulse of top industry news

This website uses cookies so that we can provide you with the best user experience possible. Cookie information is stored in your browser and performs functions such as recognising you when you return to our website and helping our team to understand which sections of the website you find most interesting and useful.
Strictly Necessary Cookie should be enabled at all times so that we can save your preferences for cookie settings.
If you disable this cookie, we will not be able to save your preferences. This means that every time you visit this website you will need to enable or disable cookies again.